Franco T.,
Too Long; Didn't Read
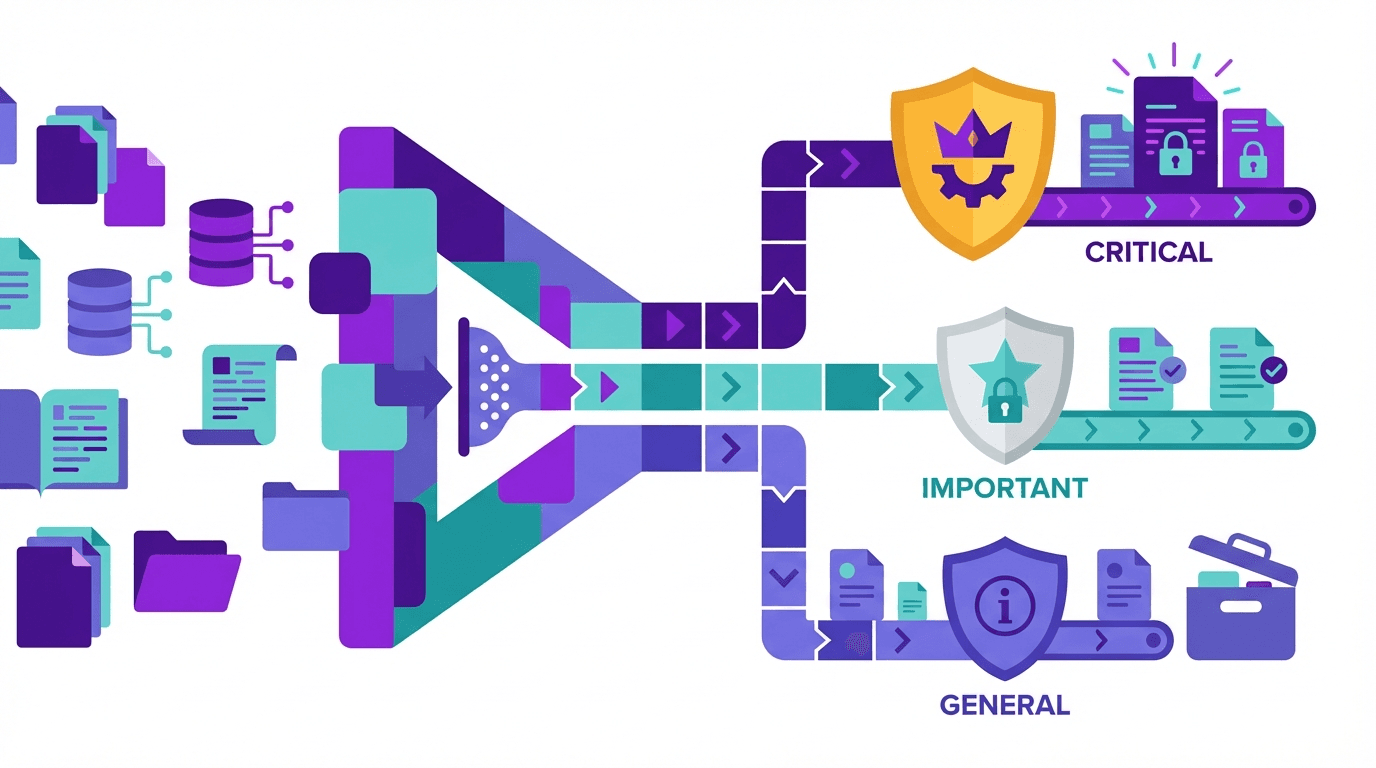
Not all data requires the same level of protection, yet most companies still treat it the same. Data classification gives you a simple framework: four levels, clear measures for each level, and you start with the most critical data. No six-month project is needed—half a day in a workshop is enough as a starting point.
You know this from your kitchen at home. In the refrigerator, meat is kept separate from vegetables, milk is not stored next to cleaning agents under the sink, and you don’t put good wine out on the balcony in the sun. No one wrote a framework for that. You do it because it is obvious that different things require different treatment.
With corporate data, this obviousness is often completely missing. We regularly encounter companies that store customer data in an open SharePoint folder while simultaneously hiding internal meeting notes behind three authentication layers. No bad intent. Simply no structure.
That is the whole problem: not a lack of awareness, but a lack of organization. And the solution is called data classification.
Why you should not postpone this
Yes, data classification sounds like a compliance box-ticking exercise. And partly, it is. But behind it lies a tangible benefit that goes beyond audits.
The regulatory argument: GDPR and nFADP require “appropriate” protective measures. What is appropriate depends on how sensitive the data is. Without classification, you cannot define “appropriate” at all. If a supervisory authority comes knocking and you have to explain why certain data was protected in one way and not another, you need a traceable structure.
ISO 27001 explicitly requires it. Annex A, Control 5.12. Anyone building an ISMS or seeking certification cannot avoid it. In our article on pragmatic ISMS implementation, we described why classification is the first concrete step there.
The budget argument: Protecting everything equally means wasting money on unimportant data while covering critical data only half-heartedly. At its core, data classification is a prioritization decision for your security budget.
What you need to do in practice
Four levels are enough: Public, Internal, Confidential, and Strictly Confidential. Some companies use three, others five. The exact number is less important than having one at all.
Capture your data landscape at a high level
Bring IT, HR, Finance, and one business unit into a room. Half a day is enough. Goal: Which data categories exist, where are they stored, and who has access? This does not have to be a complete inventory. Customer data, employee data, financial data, contracts, development data, communications, backups. That already covers 80%.
Define levels with real examples
Do not write “Confidential: data with high damage potential.” Write: “Confidential: customer lists, proposal cost calculations, HR performance data, annual financial statements before publication.” Use concrete examples from your company. Whoever later has to decide how a file should be handled does not need a philosophical definition. They need a model.
Link each level to measures
Classification without consequences is compliance theater. Here is a starting point:
Public: No special measures. May be shared.
Internal: Standard access protection, no external transmission without encryption.
Confidential: Encryption at rest and in transit, access logging, need-to-know principle.
Strictly confidential: Strict access controls, mandatory MFA, regular access reviews, no cloud storage without explicit approval.
Adapt this to your context. The list is a starting point, not a finished product.
Start with the crown jewels
You do not have to classify everything at once. Start with what would hurt most if it were lost or stolen. First the most critical data, then expand step by step. This approach delivers real value faster than trying to tackle everything at the same time.
The four mistakes everyone makes
The paper scheme. Developed in a workshop, signed by the CISO, then never looked at again. A scheme that is not integrated into everyday work does not exist.
Too many levels. Seven classification levels introduced with good intentions. After four months, no one knows what distinguishes “Confidential Level 3” from “Confidential Level 4.” Four levels are enough.
No data owners. Who decides whether a new file is “Internal” or “Confidential”? If that remains unclear, no one classifies. Or everyone does it differently. Every data category needs a clearly responsible owner.
One-time instead of continuous. Data changes. A proposal cost calculation that is confidential today may be only internally relevant after a contract is signed. Classification is a process, not a project.
A brief note on compliance alignment: once you have classified your data, a large part of the record of processing activities (ROPA) for GDPR and nFADP is already done. And anyone working toward ISO 27001 should tackle classification early. It affects controls from access control to asset management.
So: take three hours. Four to five people from IT, HR, Finance, and one business unit. Answer this together: “What are the five to ten worst data losses that could happen to us?” What comes out of that is your first classification backlog. Build from there.
If you are already facing a concrete compliance goal and do not know where to start, contact us directly. No form, no sales process. Just a conversation about what is currently burning at your organization.