Yannick H.,
Too Long; Didn't Read
An ISMS must fit the company - not the other way around. Most implementations fail not because of technology, but due to excessive scope, lack of management buy-in, and the attempt to apply enterprise frameworks to SME resources. The pragmatic approach: Start small, expand gradually, and build a system that is truly lived - not just audited.
Why Everyone is Talking About ISMS Now
Over 150,000 organizations worldwide are ISO 27001 certified. The number grows annually by 10-15%.
(ISO Survey / Industry Reports 2025)
This is not because everyone has suddenly become security enthusiasts.
70% of IT service providers in Europe and North America require ISO 27001 from their suppliers.
In other words: No ISMS, no contract. At least not with enterprise customers.
Then there are cyber insurances increasingly demanding a structured security management. And regulations like NIS2, which practically mandate an ISMS.
The question is no longer if, but how.
What an ISMS Actually Is (and What It Isn’t)
Before we get into implementation, a brief clarification.
An ISMS - Information Security Management System - is not a tool. Not software. Not a folder with policies.
An ISMS is a structured approach to managing information security.
It includes:
Governance: Who is responsible? How are decisions made?
Risk Management: What risks do we have? How do we handle them?
Controls: What measures do we implement?
Continuous Improvement: How do we learn from incidents and audits?
ISO 27001 is the most well-known standard for this - but not the only way.
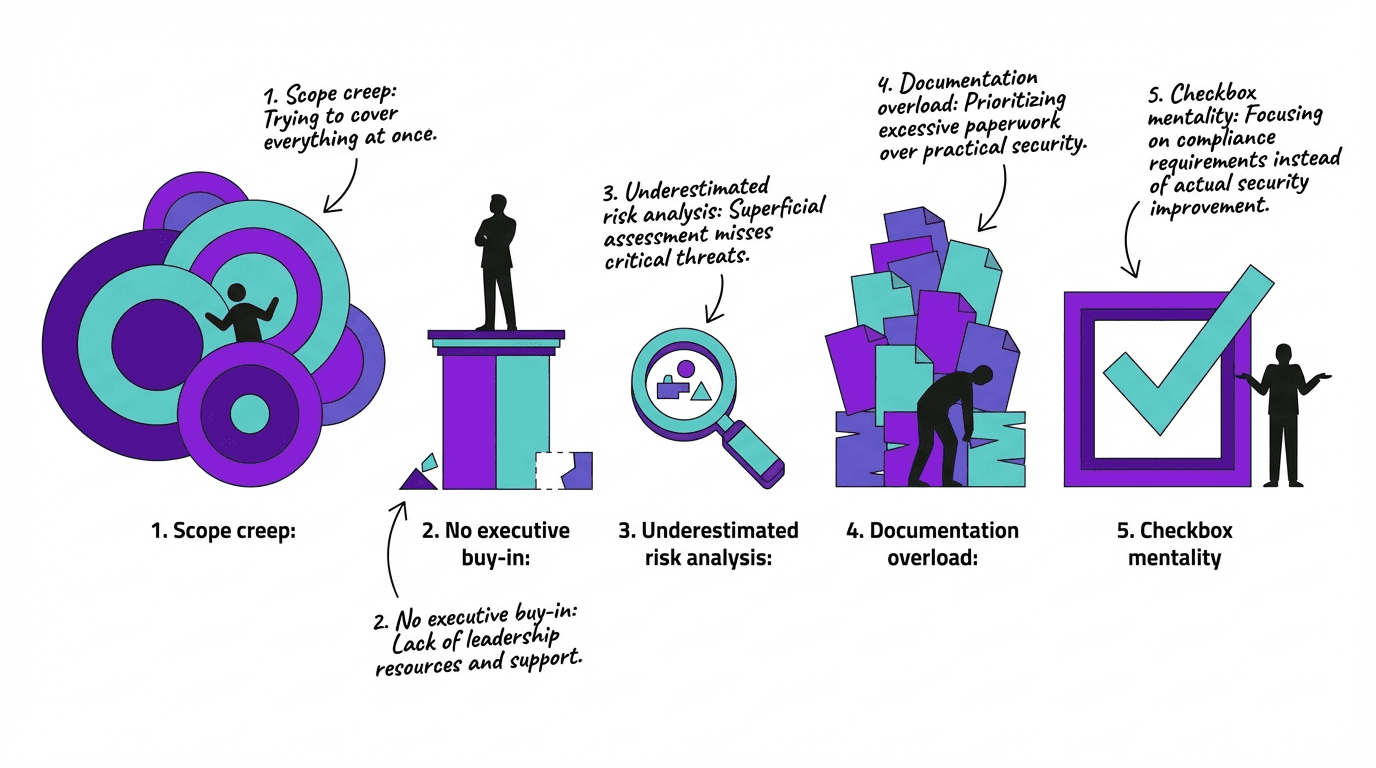
Why Most ISMS Projects Fail
Here’s the honest truth.
Most ISMS implementations don't fail due to technology. They fail due to five predictable problems.
1. Scope Too Large
The most common mistake: Wanting to certify the entire organization at once.
This works for large companies with dedicated compliance teams. For SMEs, it leads to overwhelm, delays, and eventually abandonment.
Pragmatic Approach: Start small. One department. One critical process. One location. Then expand.
2. Lack of Management Buy-in
Without top-level commitment, nothing happens. No budget. No prioritization. No enforcement.
If the executive team sees an ISMS as an "IT project," it's doomed to fail.
Pragmatic Approach: Position ISMS as a business topic. Translate risks into business language. Demonstrate ROI.
3. Underestimated Risk Analysis
The risk analysis is the heart of ISO 27001. And the part most underestimated.
It's not about creating an Excel list with 500 theoretical risks. It's about understanding and prioritizing the real risks for your company.
Pragmatic Approach: Focus on truly relevant risks. Qualitative assessment instead of pseudo-quantification. Regular updates.
4. Documentation Overload
An ISMS needs documentation. Policies, processes, proofs.
But it doesn't need 500 pages of policies that no one reads.
Pragmatic Approach: Documentation that is actually used. Short. Clear. Current. Better ten pages that are lived by than a hundred pages of shelfware.
5. Checkbox Mentality
"We need the certificate."
That's the wrong reason for an ISMS. If the goal is only the certificate, you get a system that passes audits - but provides no real security.
Pragmatic Approach: Understand ISMS as a tool, not as an end in itself. The certificate is a byproduct of good security practice.
The Pragmatic Path to ISMS
Enough about the problems. Here’s how it works.
Phase 1: Define Scope
What to include?
Not everything. At least not at the start.
Identify the area that is:
Most critical to the business
Most demanded by customers or regulations
Reasonably delimitable
This could be:
The cloud infrastructure
The customer data processing area
A specific service or product
Deliverable: A clearly defined scope with documented boundaries.
Phase 2: Capture Current State
What do we already have?
Most companies already have security measures - they are just not documented or structured.
What policies exist?
What technical controls are active?
What processes already exist?
This is not a critique exercise. This is taking stock.
Deliverable: Gap analysis between current state and ISO 27001 requirements.
Phase 3: Assess Risks
What could go wrong?
Now it gets substantial. Identify the risks for your scope:
What assets are critical?
What threats exist?
What vulnerabilities do we have?
What are the impacts if something happens?
Keep it practical. No theoretical scenarios that will never happen. Focus on what is realistic and can cause damage.
Deliverable: Risk assessment with prioritized risks and treatment plan.
Phase 4: Implement Controls
What do we do about it?
Based on the risk assessment: What measures do we need?
ISO 27001 Annex A offers 93 controls as a reference. Not all are relevant for every company.
Choose controls that:
Address your top risks
Fit your context
Are implementable with reasonable effort
Deliverable: Implemented controls with evidence.
Phase 5: Document and Live
How do we keep it running?
An ISMS is not a one-time project. It needs to be lived.
Policies that people actually read
Processes that work in everyday life
Training that sticks
Regular reviews and updates
Deliverable: Documented, functional ISMS.
What It Really Costs
Let's talk numbers.
Typical costs for SMEs:
Phase | Cost Range |
|---|---|
Gap Analysis & Consulting | CHF 10,000 - 25,000 |
Implementation & Training | CHF 15,000 - 40,000 |
Certification Audit | CHF 5,000 - 15,000 |
Annual Maintenance | CHF 3,000 - 10,000 |
It sounds like a lot. But compared to:
A data breach (average cost several million)
Lost enterprise contracts
Higher cyber insurance premiums
...it's an investment that pays off.
Organizations with mature security programs save an average of $1.9 million per security incident.
(IBM Cost of Data Breach 2025)
Key Takeaways
ISMS must fit the company. Not the other way around. A pragmatic system that is lived is better than a perfect system that only exists in audits.
Start small. The biggest mistake is too large a scope. A clearly defined area that works is better than an entire struggling organization.
Management buy-in is not optional. Without top-level commitment, the ISMS becomes an IT project - and IT projects without business support fail.
Think risk-oriented. Risk analysis is not bureaucracy - it is the core of the system. Invest time here.
Documentation that is lived. Ten pages that everyone knows are more valuable than a hundred pages no one reads.
The certificate is not the goal. It's a byproduct. The goal is a company that understands and manages information security.
If You Need Support
We help SMEs build an ISMS that works - not just is audited.
ISMS Readiness Assessment: Where do you stand? What's missing?
Pragmatic Implementation: SME-friendly approach, no enterprise overkill
Scope Definition: Finding the right starting point
CISO-as-a-Service: Continuous ISMS support without a full-time CISO
Related Articles:
Sources: